Network Radar 2 6 – Manage And Configure Network Devices

- Network Radar 2 6 – Manage And Configure Network Devices Connected
- Network Radar 2 6 – Manage And Configure Network Devices Download
- Network Radar 2 6 – Manage And Configure Network Devices Compatible
- Network Radar 2 6 – Manage And Configure Network Devices Wireless
Power Management: Lets you configure power management options for the device. When you click OK to dismiss the dialog box, the network connection’s Properties dialog box closes and you’re returned to the Network Connections page. Right-click the network adapter and choose Properties again to continue the procedure.
- Simple Network Management Protocol (SNMP) is an Internet Standard protocol for collecting and organizing information about managed devices on IP networks and for modifying that information to change device behavior. Devices that typically support SNMP include cable modems, routers, switches, servers, workstations, printers, and more.
- Manage Network Infrastructure Through a Dedicated Network. Description Manage the network infrastructure across network connections that are separated from the business use of that network, relying on separate VLANs or, even more preferable, entirely different physical connectivity for management sessions for network devices.
- For example, set all network adapter device drivers to a specific category. Then, when you create a task sequence that includes the Auto Apply Drivers step, specify a category of device drivers. Configuration Manager then scans the hardware and selects the applicable drivers from that category to stage on the system for Windows Setup to use.
Today, I will be going over Control 11 from version 7 of the top 20 CIS Controls – Secure Configuration for Network Devices, such as Firewalls, Routers, and Switches. I will go through the seven requirements and offer my thoughts on what I’ve found.
Key Takeaways for Control 11
- Leverage existing controls. If you already implemented control number 5 to monitor the configuration and change on your endpoints, then you probably already have the tools and expertise needed to address control 11. Only the final two requirements here would need additional overhead if you are implementing the controls in order.
- Network devices are computers too. These controls match exactly what you would do for any other computer in the enterprise. Don’t forget to give them attention, as well.
Requirement Listing for Control 11
1. Maintain Standard Security Configurations for Network Devices
Description: Maintain standard, documented security configuration standards for all authorized network devices.
Notes: As with control number 5, network devices also are candidates to be hardened. Both CIS and DISA have guidelines available to harden these types of devices. A tool such as Tripwire Enterprise will make this much easier.
2. Document Traffic Configuration Rules
Network Radar 2 6 – Manage And Configure Network Devices Connected
Description: All configuration rules that allow traffic to flow through network devices should be documented in a configuration management system with a specific business reason for each rule, a specific individual’s name responsible for that business need, and an expected duration of the need.
Notes: Getting the rules documented is the easy part. Tying assets and applications on those assets back to an individual or business unit is the hard part, especially for businesses which are organic. The first step is to gather the configuration and leverage the next section to alert on changes.
3. Use Automated Tools to Verify Standard Device Configuration and Detect Changes
Description: Compare all network device configurations against approved security configurations defined for each network device in use and alert when any deviations are discovered.
Antivirus zap virus & adware 3 0 1. Notes: Monitoring for change just isn’t for endpoints. Attackers can modify network device configurations to destabilize a network or allow connections in/out of the environment. A tool like Tripwire Enterprise can identify changes and report the proper administrator very quickly.
4. Install the Latest Stable Version of Any Security-related Updates on All Network Devices
Description: Install the latest stable version of any security-related updates on all network devices.
Notes: It doesn’t matter how secure your endpoints are if the firewall is using firmware from five years ago. You may be surprised at how often updates are available for these devices if you aren’t actively looking for them. By using outdated firmware, you could be leaving the front door wide open to the entire world.
5. Manage Network Devices Using Multi-Factor Authentication and Encrypted Sessions
Description: Manage all network devices using multi-factor authentication and encrypted sessions.
Notes: There are two parts to this requirement which I feel should be split out. The first is using encrypted communications to manage the devices. For example, use SSH instead of Telnet or HTTPS over HTTP. The benefits of that are well known by now. However, requiring MFA for network devices may not be supported. Even if they are, it may be overkill for the internal network. If you are doing remote administration over the internet, however, then MFA should be implemented ASAP.
6. Use Dedicated Workstations For All Network Administrative Tasks
Description: Ensure network engineers use a dedicated machine for all administrative tasks or tasks requiring elevated access. This machine shall be segmented from the organization’s primary network and not be allowed Internet access. This machine shall not be used for reading email, composing documents, or surfing the Internet.
Notes: The authors of this document are obviously worried about common attacks such as phishing, which could infect an administrator’s workstation with credential stealing malware. This is one of those requirements that is going to cause additional overhead for folks but is necessary for a more mature organization. If there are password management or network device management tools which are accessed, they should be included in this requirement, as well.
7. Manage Network Infrastructure Through a Dedicated Network
Description Manage the network infrastructure across network connections that are separated from the business use of that network, relying on separate VLANs or, even more preferable, entirely different physical connectivity for management sessions for network devices.
Notes: For the same reasons as was stated in the previous requirement, a dedicated network will reduce the chances of credential stealing malware from gaining a larger foothold on the network.
See how simple and effective security controls can create a framework that helps you protect your organization and data from known cyber attack vectors by downloading this guide here. Iphoto library manager 4 2 4 download free.
Read more about the 20 CIS Controls here:
Control 20 – Penetration Tests and Red Team Exercises
Control 19 – Incident Response and Management
Control 18 – Application Software Security
Control 17 – Implement a Security Awareness and Training Program
Blender software download 64 bit. Control 16 – Account Monitoring and Control
Control 15 – Wireless Access Control
Control 14 – Controlled Access Based on the Need to Know
Rhinoceros 5 3 2 2017. Control 13 – Data Protection
Control 12 – Boundary Defense
Control 11 – Secure Configuration for Network Devices, such as Firewalls, Routers, and Switches
Control 10 – Data Recovery Capabilities
Control 9 – Limitation and Control of Network Ports, Protocols, and Services
Control 8 – Malware Defenses
Control 7 – Email and Web Browser Protections
Control 6 – Maintenance, Monitoring, and Analysis of Audit Logs
Control 5 – Secure Configurations for Hardware and Software on Mobile Devices, Laptops, Workstations, and Servers
Control 4 – Controlled Use of Administrative Privileges
Control 3 – Continuous Vulnerability Management
Control 2 – Inventory and Control of Software Assets
Apple service toolkit 1 0 7 download free. Control 1 – Inventory and Control of Hardware Assets
You can also learn more about the CIS controls here.
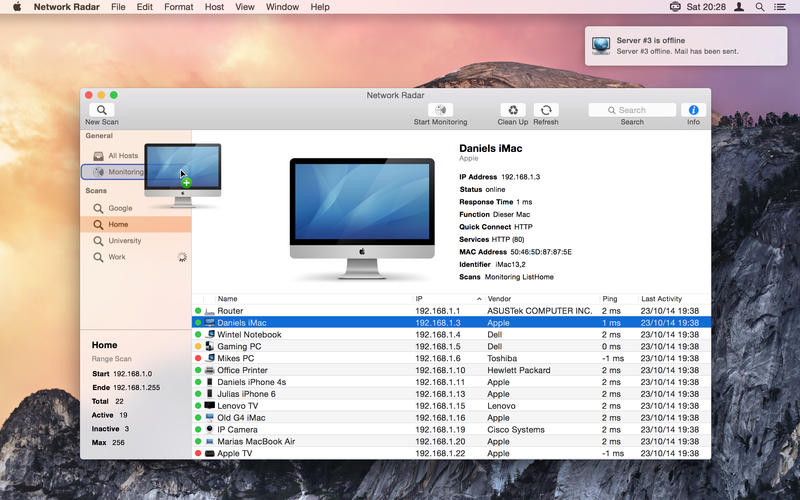
Download Network Radar 2.4 for Mac free latest version offline setup. Network Radar 2.4 for Mac is a reliable application for dealing with the management of the network and the internet.
Network Radar 2.4 for Mac Review
A professional networking application, Network Radar 2.4 comes up with a wide range of powerful tools and options to monitor the network and provides useful information. It has a straightforward user interface with a variety of powerful options that enhance the overall workflow. Also, it is very easy for the novices to operate the application. It scans the internet and gets complete information about the connected devices.
Moreover, the application provides support for exporting the reposts as CSV and TXT formats and allows the users to run different commands. The application has the possibility to run different commands and receive notifications. All in all, it is a very powerful application to deal with the network and provide useful details about the devices on the network.
Network Radar 2 6 – Manage And Configure Network Devices Download
Features of Network Radar 2.4 for Mac
Network Radar 2 6 – Manage And Configure Network Devices Compatible
- Powerful application to monitor the network
- Manage internet and the network
- Provides complete details about the network
- Simple and easy to use application
- Export the reports as XML or TXT
- Supports scanning the internet and check for the connected devices
- Use different commands and receive notifications
- Easily understandable application with straightforward options
- Retrieve complete information about the network
- Use different rules and procedures to automatically process the information
- Automatic process of the data and sending emails about the server status
- Provides complete details about the host i.e. Host, DNS, NetBIOS and the IP address etc.
- Handle the interfaces and perform numerous other operations
Technical Details of Network Radar 2.4 for Mac
- File Name: Network.Radar.v2.4.MacOSX.dmg
- File Size: 39 MB
- Developer: Witt Software

System Requirements for Network Radar 2.4 for Mac
- Mac OS X 10.11 or higher
- 500 MB free HDD
- 1 GB RAM
- Intel Processor
Network Radar 2 6 – Manage And Configure Network Devices Wireless
Network Radar 2.4 for Mac Free Download
Click on the below link to download the latest offline setup of Network Radar 2.4 for Mac OS X. You can also download iNet Network Scanner 2.4.

Network Radar 2 6 – Manage And Configure Network Devices
UNDER MAINTENANCE